Security
We bring online combat experience and defence expertise in both military & governmental sectors
Our company is built on experience in various sectors. From engaging national cyber-attacks to remediation of high-profile incidents. We have experience dealing with APT & other threats in even the most complex and restricted environments. Our defense experience comes second only to our attack expertise. We tackle security incidents daily such as Ransom & Extortion, Red Team assessment, Incident response as well as Cyber intelligence gathering and Blue team.
Our Services
-
RED TEAM
See your business through the eyes of your attackers.
LEARN MORE
Our Red Team will prevent and provide remediation suggestions &recommendations against a real-world attack.
-
Security Consulting
Our consulting department, Consists of leaders of their fields, brings vast knowledge and experience to protect your organization.
LEARN MORE
-
Blue Team
A Blue Team will consist of incident response, Malware & SOC Analysis.
LEARN MORE
Our Blue Team will not only close a breach but also proactively prevent future threats.
-
Cyber Intelligence
Our cyber intelligence professionals will enrich your team`s security knowledge, arsenal, tools and capabilities. By staying ahead of the curve and proactively avoid real world threats
LEARN MORE
-
Social Engineering
Our team of experienced hackers will provide a full social engineering campaign on multiple layers to insure you understand your organizational weaknesses and proactively rid them.
LEARN MORE
-
SOC CONSULTING
The first line of defense
LEARN MORE
Our Team will provide you with years of hands-on experience and proactively prevent treats and dangers.
Gamified Cyber Security Training Simulator
Practice Your Teams In Hands-on, Cutting-edge, Real-world
Incidents
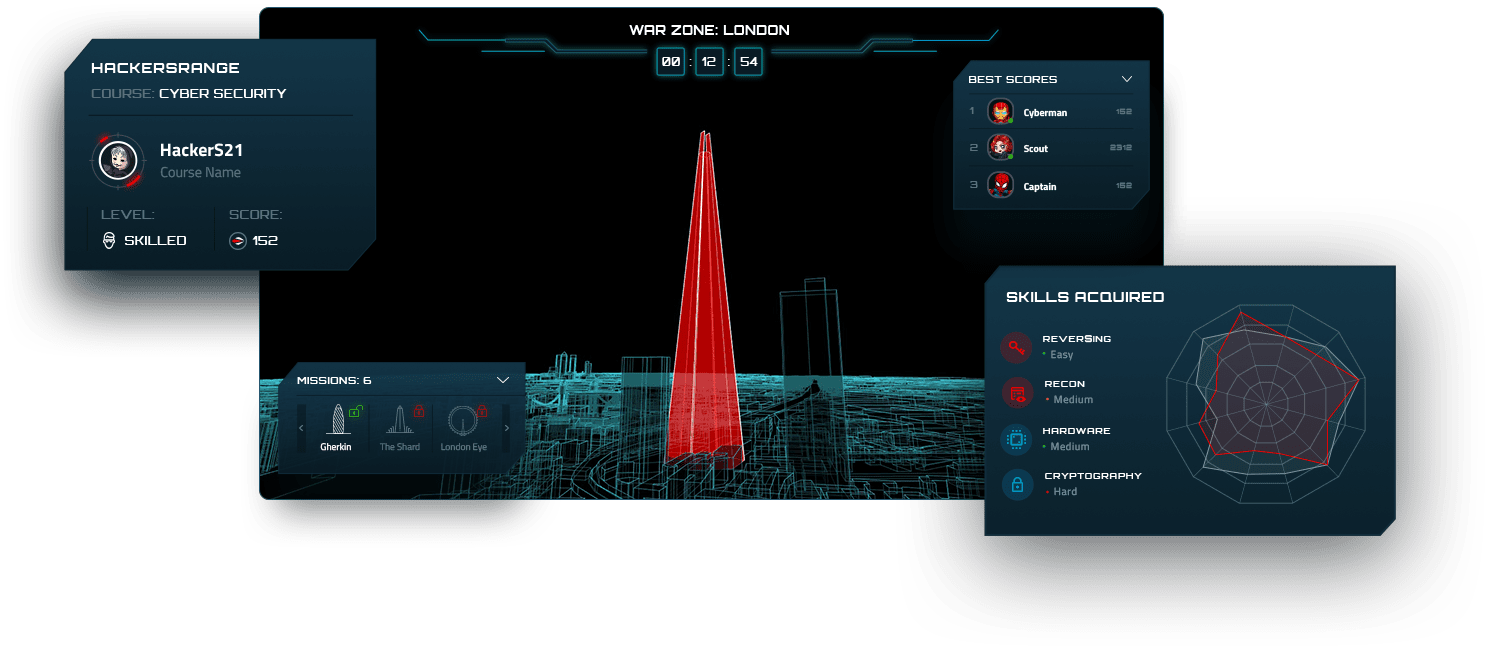
USERS WILL
Experience training in highly complex real-world environments

Practice Hand-on Cutting-edge Cyber Security Offensive & Defensive Scenarios
Gain Knowledge & Skills in an immersive Gamified Simulator
Accelerate the process of gaining experience by increasing exposure to incidents & challenges

Amongst Our Clients





Last Articles
-

MuddyWater’s Cyber Assaults on Israel
This blog details MuddyWater’s intensified cyber operations against Israeli infrastructure, highlighting their use of sophisticated tactics, and providing detection and mitigation strategies. -

CheckMesh: Hidden Threats in Your FW
CheckMesh attack: APTs turning Check Point firewalls into Command & Control nodes. Learn how we uncovered and mitigated this threat. -
A work of Art, it’s One of the most sophisticated exploits we have ever seen.
Dean Bar, HackersEye COO & Co- Founder In a special interview to “Haaretz” newspaper explaining how NSOs spyware “Pegasus” has managed to hack target’s Apple’s IOS iPhones. -
LOG4J exploit shocks cyber security community.
Organizations should assume that they have already been hacked.” Dean Bar HackersEye COO& Cyber Security specialist in an interview for “The Marker”. -

Highly skilled Iranian hackers claim to have hacked intel Israel.
Hackers group that goes by the name Pay2Key have published a ransom demand at their twitter account. -

HackersEye lead a first of its kind training with Israeli National Cyber Directorate.
HackersEye team introduce their Hands-On Cyber training simulator: “HackersRange”, and train over 50 Cyber Security analysts from Israel’s finest institutions and organizations.